How to Crack WiFi Password (Hack Wi-Fi Network)
⚡ Smart Summary
Cracking WiFi passwords reveals how wireless networks become exposed through weak encryption and flawed authentication. This overview explains how WEP, WPA, and WPA2 operate, the tools attackers use, and the controls administrators should enforce to mitigate unauthorized wireless access.
Wireless networks are accessible to anyone within the router’s transmission radius. This makes them vulnerable to attack. Hotspots are available in public places such as airports, restaurants, and parks. In this tutorial, we will introduce common techniques used to exploit weaknesses in wireless network security implementations. We will also look at countermeasures you can put in place to protect against such attacks.
What is a Wireless Network?
A wireless network uses radio waves to link computers and other devices together. The implementation is done at Layer 1 (the physical layer) of the OSI model. Because these signals propagate through the air, any receiver tuned to the right frequency and within range can pick them up, which is why authentication and encryption are essential.
How to Access a Wireless Network?
You will need a wireless-enabled device such as a laptop, tablet, or smartphone, and you must be within the transmission radius of a wireless access point. Most devices display a list of available networks when Wi-Fi is on. If the network is open, you simply tap Connect. If it is password protected, you will need the passphrase to gain access.
Wireless Network Authentication
Because a wireless network is accessible to anyone with a Wi-Fi enabled device, most networks are password protected. Below are the most commonly used authentication techniques.
WEP
WEP is the acronym for Wired Equivalent Privacy. It was developed in 1997 for IEEE 802.11 WLAN standards with the goal of providing privacy equivalent to wired networks. WEP encrypts data transmitted over the network to keep it safe from eavesdropping. However, WEP was officially deprecated by the IEEE in 2004 due to serious cryptographic weaknesses.
WEP Authentication
WEP supports two authentication methods:
- Open System Authentication (OSA) – Grants access to any station requesting authentication based on the configured access policy, without verifying a shared secret.
- Shared Key Authentication (SKA) – Sends an encrypted challenge to the station requesting access. The station encrypts the challenge with its key and responds. If the value matches what the access point expects, access is granted.
WEP Weakness
WEP has significant design flaws that an attacker can exploit:
- The packet integrity check uses Cyclic Redundancy Check (CRC32), which can be compromised by capturing at least two packets. Attackers can modify bits in the encrypted stream and checksum so the packet is accepted by the authentication system.
- WEP uses the RC4 stream cipher with an initialization value (IV) and a secret key. The IV is only 24 bits, while the secret key is 40 or 104 bits. The short key makes brute-force feasible.
- Weak IV combinations do not encrypt sufficiently, making them vulnerable to statistical attacks such as the FMS attack.
- Because WEP is password-based, it is vulnerable to dictionary attacks.
- Key management is poorly implemented; WEP has no centralized key management system.
- Initialization values can be reused within the same session.
Because of these flaws, WEP has been deprecated in favor of WPA, WPA2, and WPA3.
WPA
WPA is the acronym for Wi-Fi Protected Access. It is a security protocol developed by the Wi-Fi Alliance in 2003 in response to weaknesses found in WEP. WPA uses larger 48-bit initialization values (instead of 24 bits in WEP) and introduces temporal keys via TKIP to rotate the per-packet encryption key.
WPA Weaknesses
- The collision avoidance implementation can be broken under specific conditions.
- It is vulnerable to denial-of-service attacks that force deauthentication.
- Pre-shared keys use passphrases; weak passphrases are vulnerable to dictionary and brute-force attacks.
WPA2 and WPA3: Modern Wi-Fi Security Standards
WPA2 replaced the original WPA in 2004 and introduced AES with CCMP, delivering far stronger confidentiality and integrity protection. WPA2-Personal uses a pre-shared key, while WPA2-Enterprise uses 802.1X with a RADIUS server for per-user credentials.
WPA3, released in 2018, addresses residual weaknesses in WPA2. It replaces the four-way handshake with Simultaneous Authentication of Equals (SAE), which resists offline dictionary attacks. WPA3 also enables forward secrecy and mandates Protected Management Frames.
| Standard | Year | Encryption | Key Exchange | Status |
|---|---|---|---|---|
| WEP | 1997 | RC4 | Static key | Deprecated |
| WPA | 2003 | RC4 + TKIP | PSK | Deprecated |
| WPA2 | 2004 | AES-CCMP | PSK / 802.1X | Widely used |
| WPA3 | 2018 | AES-GCMP | SAE / 802.1X | Recommended |
General Attack Types
Before exploring specific cracking workflows, understand the underlying attack categories wireless adversaries rely on:
- Sniffing – Intercepting packets as they are transmitted over the air. Captured frames can be decoded with tools such as Cain & Abel or Wireshark.
- Man in the Middle (MITM) Attack – Eavesdropping on a session and relaying or altering traffic between the victim and the access point.
- Denial of Service (DoS) Attack – Flooding or deauthenticating legitimate clients. Utilities such as FataJack were historically used for this purpose.
How to Crack WiFi (Wireless) Networks
WEP Cracking
Cracking is the process of exploiting weaknesses in wireless networks to gain unauthorized access. WEP cracking targets networks still using WEP and falls into two categories:
- Passive cracking – No effect on network traffic until the WEP key is recovered. It is difficult to detect.
- Active cracking – Injects packets, raising network load. Easier to detect but more effective and faster.
How to Hack WiFi Password
In this practical scenario, we will recover a wireless credential from a Windows machine using Cain and Abel, a legacy penetration testing utility. Cain and Abel has not been officially maintained since 2014; it is shown here for educational purposes and works best on older Windows releases.
Decoding Wireless Network Passwords Stored in Windows
Step 1) Download the Cain and Abel tool.
Install Cain & Abel from a trusted archive and launch the application.
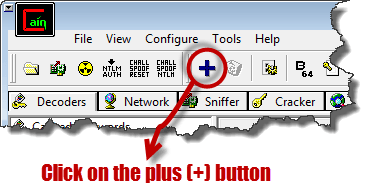
Step 2) Select the Decoders tab and choose Wireless Passwords.
Select the Decoders tab, click Wireless Passwords in the left navigation, and click the plus (+) button to scan for stored credentials.
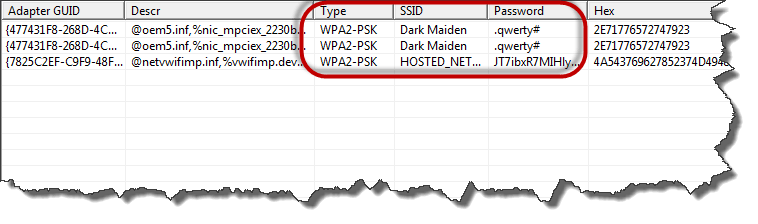
Step 3) Review the recovered passwords.
If the host has connected to a secured wireless network before, Cain and Abel displays results similar to those below.
Step 4) Capture SSID, encryption type, and passphrase.
The decoder shows the encryption type, SSID, and plaintext password used, which is what an attacker would export for follow-on attacks.
How to Hack WiFi Password using Hacker (WEP Cracking) Tools
Penetration testers use several utilities to audit WEP-protected networks:
- Aircrack-ng – Network sniffer and WEP/WPA cracker: https://www.aircrack-ng.org/.
- WEPCrack – Open-source 802.11 WEP key recovery program implementing the FMS attack: https://wepcrack.sourceforge.net/.
- Kismet – Detects visible and hidden wireless networks, sniffs packets, and flags intrusions: https://www.kismetwireless.net/.
- WebDecrypt – Uses active dictionary attacks to crack WEP keys: https://wepdecrypt.sourceforge.net/.
WPA Cracking
WPA uses a 256-bit pre-shared key derived from the passphrase. Short or common passphrases are vulnerable to dictionary attacks and rainbow-table lookups. Common tools include:
- CoWPAtty – Brute-force and dictionary attacks against WPA pre-shared keys. Bundled with Kali Linux.
- Cain & Abel – Decodes capture files from sniffers such as Wireshark, which may contain WEP or WPA-PSK frames: https://www.softpedia.com/get/Security/Decrypting-Decoding/Cain-and-Abel.shtml.
Cracking Wireless Network WEP/WPA Keys
It is possible to crack WEP and WPA keys to gain access to a wireless network. Success depends on software, compatible hardware, patience, and how actively the target network users are transmitting data.
Kali Linux is the modern successor to BackTrack (retired in 2013). Built on Debian, Kali ships with a curated collection of security tools including:
- Metasploit
- Wireshark
- Aircrack-ng
- NMap
- Ophcrack
At a minimum, cracking wireless keys requires:
- Wireless adapter with packet-injection support (such as an Alfa AWUS036ACH).
- Kali Linux: https://www.kali.org/get-kali/.
- Proximity to the target – Active users improve your chances of collecting usable packets.
- Linux knowledge and familiarity with Aircrack-ng scripts.
- Patience – Recovery may take minutes to many hours depending on passphrase complexity.
How to Secure Wi-Fi Leaks
To reduce wireless network exposure, organizations should adopt the following controls:
- Change the default administrator password and SSID that ship with the hardware.
- Enable the strongest available authentication, preferring WPA3 and falling back to WPA2 for legacy clients.
- Restrict access by allowing only registered MAC addresses (a hardening layer, not a primary control).
- Use strong WPA-PSK keys that combine symbols, numbers, and mixed-case letters to resist dictionary and brute-force attacks.
- Deploy firewalls and network segmentation to limit lateral movement after any unauthorized association.
- Disable WPS and patch router firmware regularly to close known vulnerabilities.
How AI Enhances Wi-Fi Network Security and Attack Detection
Artificial intelligence has become a practical layer inside modern Wi-Fi defenses. Because wireless networks generate huge volumes of telemetry from association events, probe requests, and traffic flows, AI models surface hostile behavior far faster than rule-based monitoring. Administrators now rely on AI-assisted platforms to supplement intrusion detection systems and reduce mean time to respond.
Here is how AI strengthens wireless security programs:
- Anomaly Detection: Unsupervised models learn a baseline of normal behavior (roaming patterns, data volume, protocol mix) and flag deauthentication floods, rogue access points, or evil twin impersonation.
- Behavioral Authentication: AI correlates device fingerprints, signal strength, and time-of-day usage to confirm a client is the legitimate user, not a stolen-credential attacker.
- Automated Passphrase Audits: Generative models predict human-chosen passphrases, letting red teams run smarter dictionary attacks so weak keys are retired before criminals find them.
- Real-Time Threat Triage: SIEM platforms feed wireless events into classifiers that score risk, cluster alerts, and suppress noise that would overwhelm analysts.
- Adaptive Response: AI-driven network access control can quarantine a suspicious endpoint, demand re-authentication, or steer it onto a restricted VLAN automatically.
Attackers also apply AI to fingerprint devices, accelerate handshake cracking, and craft convincing captive-portal phishing pages. Pair AI-powered monitoring with WPA3, strong passphrases, and disciplined patching so automated defense keeps pace with automated offense.