What is Vulnerability Testing? VAPT Scan Assessment Tool
Vulnerability Testing
Vulnerability Testing also called Vulnerability Assessment is a process of evaluating security risks in software systems to reduce the probability of threats. The purpose of vulnerability testing is reducing the possibility for intruders/hackers to get unauthorized access of systems. It depends on the mechanism named Vulnerability Assessment and Penetration Testing (VAPT) or VAPT testing.
A vulnerability is any mistake or weakness in the system’s security procedures, design, implementation or any internal control that may result in the violation of the system’s security policy.
Why do Vulnerability Assessment
- It is important for the security of the organization.
- The process of locating and reporting the vulnerabilities, which provide a way to detect and resolve security problems by ranking the vulnerabilities before someone or something can exploit them.
- In this process Operating systems, Application Software and Network are scanned in order to identify the occurrence of vulnerabilities, which include inappropriate software design, insecure authentication, etc.
Vulnerability Assessment Process
Here is the step by step Vulnerability Assessment Process to identify the system vulnerabilities.
Step 1) Goals & Objectives : – Define goals and objectives of Vulnerability Analysis.
Step 2) Scope : – While performing the Assessment and Test, Scope of the Assignment needs to be clearly defined.
The following are the three possible scopes that exist:
- Black Box Testing : – Testing from an external network with no prior knowledge of the internal network and systems.
- Grey Box Testing: – Testing from either external or internal networks with the knowledge of the internal network and system. It’s the combination of both Black Box Testing and White Box Testing.
- White Box Testing : – Testing within the internal network with the knowledge of the internal network and system. Also known as Internal Testing.
Step 3) Information Gathering : – Obtaining as much information about IT environment such as Networks, IP Address, Operating System Version, etc. It’s applicable to all the three types of Scopes such as Black Box Testing, Grey Box Testing and White Box Testing.
Step 4) Vulnerability Detection : – In this process, vulnerability scanners are used to scan the IT environment and identify the vulnerabilities.
Step 5) Information Analysis and Planning : – It will analyze the identified vulnerabilities to devise a plan for penetrating into the network and systems.
ManageEngine Vulnerability Manager Plus is a powerful vulnerability assessment and management tool that provides end-to-end coverage for vulnerability scanning, detection, assessment, and remediation. It helps organizations proactively identify security weaknesses across their network, prioritize threats based on risk severity, and automate patch deployment to strengthen their security posture.
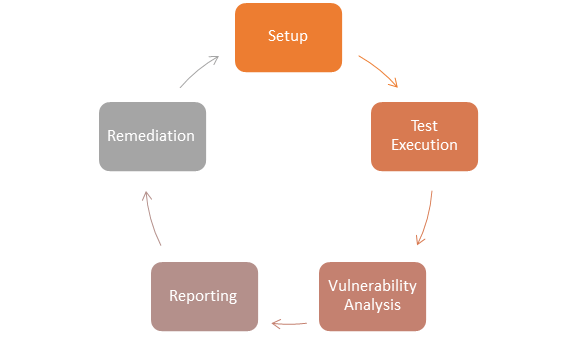
How to do Vulnerability Assessment
Following is the step by step process on How to do Vulnerability Assessment:
Step 1) Setup
- Begin Documentation
- Secure Permissions
- Update Tools
- Configure Tools
Step 2) Test Execution
- Run the Tools
- Run the captured data packet (A packet is the unit of data that is routed between an origin and the destination. When any file, for example, e-mail message, HTML file, Uniform Resource Locator(URL) request, etc. is sent from one place to another on the internet, the TCP layer of TCP/IP divides the file into a number of “chunks” for efficient routing, and each of these chunks will be uniquely numbered and will include the Internet address of the destination. These chunks are called packets. When all the packets are arrived, they will be reassembled into the original file by the TCP layer at the receiving end while running the assessment tools
Step 3) Vulnerability Analysis
- Defining and classifying network or System resources.
- Assigning priority to the resources( Ex: – High, Medium, Low)
- Identifying potential threats to each resource.
- Developing a strategy to deal with the most prioritized problems first.
- Defining and implementing ways to minimize the consequences if an attack occurs.
Step 4) Reporting
Step 5) Remediation
- The process of fixing the vulnerabilities.
- Performed for every vulnerability
Types of a vulnerability scanner
Host Based
- Identifies the issues in the host or the system.
- The process is carried out by using host-based scanners and diagnose the vulnerabilities.
- The host-based tools will load a mediator software onto the target system; it will trace the event and report it to the security analyst.
Network-Based
- It will detect the open port, and identify the unknown services running on these ports. Then it will disclose possible vulnerabilities associated with these services.
- This process is done by using Network-based Scanners.
Database-Based
- It will identify the security exposure in the database systems using tools and techniques to prevent from SQL Injections. (SQL Injections: – Injecting SQL statements into the database by the malicious users, which can read the sensitive data’s from a database and can update the data in the Database.)
Tools for Vulnerability Scanning
1) Teramind
Teramind delivers a comprehensive suite for insider threat prevention and employee monitoring. It enhances security through behavior analytics and data loss prevention, ensuring compliance and optimizing business processes. Its customizable platform suits various organizational needs, providing actionable insights that focus on boosting productivity and safeguarding data integrity.
Features:
- Insider Threat Prevention: Detects and prevents user actions that may indicate insider threats to data.
- Business Process Optimization: Utilizes data-driven behavior analytics to redefine operational processes.
- Workforce Productivity: Monitors productivity, security, and compliance behaviors of the workforce.
- Compliance Management: Helps manage compliance with a single, scalable solution suitable for small businesses, enterprises, and government agencies.
- Incident Forensics: Provides evidence to enrich incident response, investigations, and threat intelligence.
- Data Loss Prevention: Monitors and protects against the potential loss of sensitive data.
- Employee Monitoring: Offers capabilities to monitor employee performance and activities.
- Behavioral Analytics: Analyzes granular customer app behavior data for insights.
- Customizable Monitoring Settings: Allows customization of monitoring settings to suit specific use cases or to implement predefined rules.
- Dashboard Insights: Provides visibility and actionable insights into workforce activities through a comprehensive dashboard.
| Category | Tool | Description |
|---|---|---|
| Host Based | STAT | Scan multiple systems in the network. |
| TARA | Tiger Analytical Research Assistant. | |
| Cain & Abel | Recover password by sniffing network, cracking HTTP password. | |
| Metasploit | Open source platform for developing, testing and exploit code. | |
| Network-Based | Cisco Secure Scanner | Diagnose and Repair Security Problems. |
| Wireshark | Open Source Network Protocol Analyzer for Linux and Windows. | |
| Nmap | Free Open Source utility for security auditing. | |
| Nessus | Agentless auditing, Reporting and patch management integration. | |
| Database-Based | SQL diet | Dictionary Attack tool door for SQL server. |
| Secure Auditor | Enable user to perform enumeration, scanning, auditing, and penetration testing and forensic on OS. | |
| DB-scan | Detection of Trojan of a database, detecting hidden Trojan by baseline scanning. |
Advantages of Vulnerability Assessment
- Open Source tools are available.
- Identifies almost all vulnerabilities
- Automated for Scanning.
- Easy to run on a regular basis.
Disadvantages of Vulnerability Assessment
- High false positive rate
- Can easily detect by Intrusion Detection System Firewall.
- Often fail to notice the latest vulnerabilities.
Comparison of Vulnerability Assessment and Penetration Testing
| Vulnerability Assessment | Penetration Testing | |
|---|---|---|
| Working | Discover Vulnerabilities | Identify and Exploit Vulnerabilities |
| Mechanism | Discovery & Scanning | Simulation |
| Focus | Breadth over Depth | Depth over Breadth |
| Coverage of Completeness | High | Low |
| Cost | Low- Moderate | High |
| Performed By | In-house Staff | An attacker or Pen Tester |
| Tester Knowledge | High | Low |
| How often to Run | After each equipment is loaded | Once in a year |
| Result | Provide Partial Details about Vulnerabilities | Provide Complete Details of Vulnerabilities |
Vulnerability Testing Methods
Active Testing
- Inactive Testing, a tester introduces new vulnerability assessment test data and analyzes the results.
- During the testing process, the testers create a mental model of the process, and it will grow further during the interaction with the software under test.
- While doing the test, the tester will actively involve in the process of finding out the new test cases and new ideas. That’s why it is called Active Testing.
Passive Testing
- Passive testing, monitoring the result of running software under test without introducing new test cases or data
Network Testing
- Network Testing is the process of measuring and recording the current state of network operation over a period of time.
- Testing is mainly done for predicting the network operating under load or to find out the problems created by new services.
- We need to Test the following Network Characteristics:-
- Utilization levels
- Number of Users
- Application Utilization
Distributed Testing
- Distributed Tests are applied for testing distributed applications, which means, the applications that are working with multiple clients simultaneously. Basically, testing a distributed application means testing its client and server parts separately, but by using a distributed testing method, we can test them all together.
- The test parts, including those involved in the vulnerable test, will interact with each other during the Test Run. This makes them synchronized in an appropriate manner. Synchronization is one of the most crucial points in distributed testing.
Conclusion
In Software Engineering, vulnerable testing depends upon two mechanisms namely Vulnerability Assessment and Penetration Testing. Both these tests differ from each other in strength and tasks that they perform. However, to achieve a comprehensive report on Vulnerability Testing, the combination of both procedures is recommended. To find the right tools for these tasks, consider exploring these penetration testing tools.