Password Cracker: How to Crack/Guess a Password
⚡ Smart Summary
Password cracking is the practice of recovering credentials by systematically guessing, comparing, or computing them against stored hashes. This overview explains how attackers operate, the tools they use, the strength factors that resist them, and the controls administrators must enforce.
Password cracking is one of the oldest disciplines in offensive security, yet it remains as relevant as ever because users continue to choose predictable secrets. In this tutorial, we will introduce the common techniques attackers use to recover passwords, the tools that automate the work, and the countermeasures administrators can deploy to protect systems against these attacks.
What is Password Cracking?
Password cracking is the process of attempting to gain unauthorized access to a restricted system by recovering the secret that protects an authentication mechanism. The cracking process can involve comparing stored password hashes against a precomputed word list or running algorithms that generate candidate passwords until a match is found. Once a match is discovered, the attacker can authenticate as a legitimate user without ever guessing online.
What is Password Strength?
Password strength is the measure of a password’s efficiency to resist password cracking attacks. The strength of any password is determined by three properties:
- Length: the total number of characters the password contains.
- Complexity: whether it uses a combination of uppercase letters, lowercase letters, numbers, and symbols.
- Unpredictability: whether the password can be guessed easily by an attacker who knows the user.
Let us compare three passwords: password, password1, and #password1$. For this example, we will use the password strength indicator of cPanel. The images below show the strength of each candidate.
Note: the password used is password; the strength is 1, which is very weak.
Note: the password used is password1; the strength is 28, which is still weak.
Note: the password used is #password1$; the strength is 60, which is strong. The higher the strength number, the better the password.
Now suppose we have to store the same passwords using MD5 hashing. We will use an online MD5 hash generator to convert each password into its hash value. The table below shows the resulting hashes.
| Password | MD5 Hash | cPanel Strength Indicator |
|---|---|---|
| password | 5f4dcc3b5aa765d61d8327deb882cf99 | 1 |
| password1 | 7c6a180b36896a0a8c02787eeafb0e4c | 28 |
| #password1$ | 29e08fb7103c327d68327f23d8d9256c | 60 |
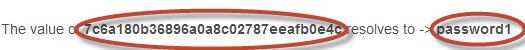
We will now use a public MD5 reverse-lookup site to crack the above hashes. The images below show the password cracking results for each value.
As you can see from the above results, we managed to crack the first and second passwords, which had lower strength numbers. We did not manage to crack the third password, which was longer, more complex, and unpredictable. It also had a higher strength number.
Password Cracking Techniques
There are several proven techniques attackers use to recover passwords. We will describe the most commonly used categories below.
- Dictionary attack: This method uses a wordlist of likely candidates and compares each one against captured user passwords or password hashes.
- Brute force attack: Brute force attacks combine alphanumeric characters and symbols using algorithms to systematically generate every possible password until a match is found. For example, a password such as password can also be tried as p@$$word using a hybrid brute force rule.
- Rainbow table attack: This method relies on precomputed hashes. Suppose a database stores passwords as MD5 hashes. The attacker creates another table that stores MD5 hashes of common passwords and compares the captured hash against the precomputed table. If a match is found, the password is recovered.
- Guess: As the name suggests, this method involves guessing. Passwords such as qwerty, password, and admin are commonly used or set as defaults. If they have not been changed, they can be compromised quickly.
- Spidering: Most organizations use passwords that contain company information. This information can be harvested from corporate websites and social media such as Facebook and Twitter. Spidering gathers data from these sources to build targeted wordlists, which are then used in dictionary and brute force attacks.
- Credential stuffing: Attackers replay username and password pairs leaked from one breach against unrelated services, exploiting users who reuse credentials.
A spidering wordlist for a fictional company might combine: 1976 (founder birth year); smith, jones (surnames); acme (company name); built, to, last (vision keywords); golfing, chess, soccer (hobbies).
The table below compares techniques by speed, prerequisites, and detectability.
| Technique | Speed | Requires Hash? | Detectable Online? |
|---|---|---|---|
| Dictionary | Fast | Optional | Yes |
| Brute force | Slow | Optional | Yes |
| Rainbow table | Very fast | Yes | No (offline) |
| Guessing | Variable | No | Yes |
| Spidering | Slow | No | Yes |
| Credential stuffing | Fast | No | Yes |
Password Cracker Tools
Password cracker tools are software programs that automate the techniques described above. We already touched on one such utility in the strength example earlier, where a public MD5 lookup uses a rainbow table to reverse common hashes. We will now look at additional tools that practitioners rely on during authorized assessments.
1) John the Ripper
John the Ripper uses the command prompt and accepts wordlists with rules to generate candidates. It auto-detects many common hash formats. The program is free, while curated commercial wordlists are available separately. Visit https://www.openwall.com/john/.
2) Cain & Abel
Cain & Abel runs on Windows and recovers user passwords, performs network sniffing, and more. Its graphical interface makes it popular with newcomers. The tool has not been actively maintained since 2014, so use it only on legacy lab systems. See https://sectools.org/tool/cain/.
3) Ophcrack
Ophcrack is a cross-platform Windows password cracker that uses rainbow tables. It runs on Windows, Linux, and macOS, and includes a brute force module. Visit https://ophcrack.sourceforge.io/.
4) Hashcat
Hashcat is the modern standard for offline password recovery. It supports 300+ hash algorithms, leverages GPU acceleration, and offers rule-based attacks. Documentation lives at https://hashcat.net/hashcat/.
5) Hydra
Hydra (THC-Hydra) targets online services such as SSH, FTP, RDP, and HTTP login forms. It ships with Kali Linux and is widely used in authorized red-team operations.
How to Protect Against Password Cracking Attacks?
An organization can use the following measures to reduce the chances of passwords being cracked:
- Require a minimum of 12 characters and avoid predictable patterns such as 11552266 or qwerty1234.
- Store passwords with a slow one-way hash function such as bcrypt, scrypt, or Argon2 rather than fast hashes such as MD5 or SHA-1.
- Salt every password before hashing; salts defeat rainbow table lookups even when the hash itself is fast.
- Adopt password policies that favor high strength scores and promote passphrases, as recommended by NIST SP 800-63B.
- Enable multi-factor authentication (MFA) so a stolen password alone does not grant access.
- Use a password manager to generate unique credentials for every service, neutralizing credential stuffing attacks.
- Configure account lockout, throttling, and continuous monitoring to detect online brute force activity early.
Hacking Activity: Hack Now!
In this practical scenario, we are going to crack a Windows account that uses a simple password. Windows stores local credentials as NTLM hashes (an MD4-based scheme), and we will use the NTLM cracker module in Cain and Abel to recover the value.
Cain and Abel can crack passwords using a dictionary attack, brute force, or cryptanalysis (precomputed tables). We will use the dictionary attack here. Download the wordlist 10k-Most-Common.zip from a reputable mirror. For this demonstration, we created an account called Accounts with the password qwerty on a Windows 7 lab machine.
How to Crack a Password
The walkthrough below pairs each Cain and Abel screen with the action to take. Follow the steps in order against your own lab account, never against a system you do not own.
Step 1) Open Cain and Abel.
Launch the application; you will see the following main screen.
Step 2) Find the Add button.
Make sure the Cracker tab is selected as shown above and click the Add button on the toolbar.
Step 3) Choose the import source.
The following dialog window appears. Select Import Hashes from local system and click Next.
Step 4) Review the imported accounts.
Local user accounts are listed as follows. The exact results will reflect the user accounts on your lab machine.
Step 5) Right-click the target account.
Right-click the account you want to crack. For this tutorial, we will use the Accounts user.
Step 6) Open the dictionary attack panel.
In the dictionary attack window, right-click in the dictionary section and select Add to list as shown below.
Step 7) Browse to the wordlist file.
Browse to the 10k-most-common.txt file you just downloaded and select it.
Step 8) Review the recovered password.
If the user chose a simple password such as qwerty, you will see results similar to the screen below, with the cleartext value next to the user account.
Note: the time taken to crack a password depends on the password strength, the complexity of the candidate list, and the processing power of your machine. If the dictionary attack does not recover the password, try a brute force or cryptanalysis attack next.
How AI Is Reshaping Password Cracking and Defense
Artificial intelligence has become a serious force on both sides of password cracking. Attackers train language models on leaked credential dumps to predict realistic passphrases, while defenders pair the same models with telemetry pipelines to detect compromise faster.
Here is how AI is changing the field today:
- Smarter Wordlist Generation: Generative models such as PassGAN learn human password patterns and produce candidate lists that crack more hashes than static dictionaries.
- Behavioral Risk Scoring: Defensive AI inspects login geography, device fingerprint, and typing rhythm, sending unusual contexts to step-up authentication.
- Real-Time Anomaly Detection: Machine learning classifiers watch authentication logs and flag credential stuffing or slow brute force campaigns that signature rules miss.
- Automated Policy Coaching: Identity platforms grade new passphrases against organization-specific corpora and suggest stronger replacements before users finalize them.
- Phishing-Resistant Defense: AI accelerates the rollout of FIDO2 and passkey flows by analyzing risk signals and reducing user friction.
Pair AI monitoring with multi-factor authentication, modern hashing such as Argon2, and rapid breach-notification feeds to keep automated defense ahead of automated offense.