Penetration Testing Tutorial: What is PenTest?
Penetration Testing
Penetration Testing or Pen Testing is a type of Security Testing used to cover vulnerabilities, threats and risks that an attacker could exploit in software applications, networks or web applications. The purpose of penetration testing is to identify and test all possible security vulnerabilities that are present in the software application. Penetration testing is also called Pen Test.
Vulnerability is the risk that an attacker can disrupt or gain authorized access to the system or any data contained within it. Vulnerabilities are usually introduced by accident during software development and implementation phase. Common vulnerabilities include design errors, configuration errors, software bugs etc. Penetration Analysis depends upon two mechanisms namely Vulnerability Assessment and Penetration Testing(VAPT).
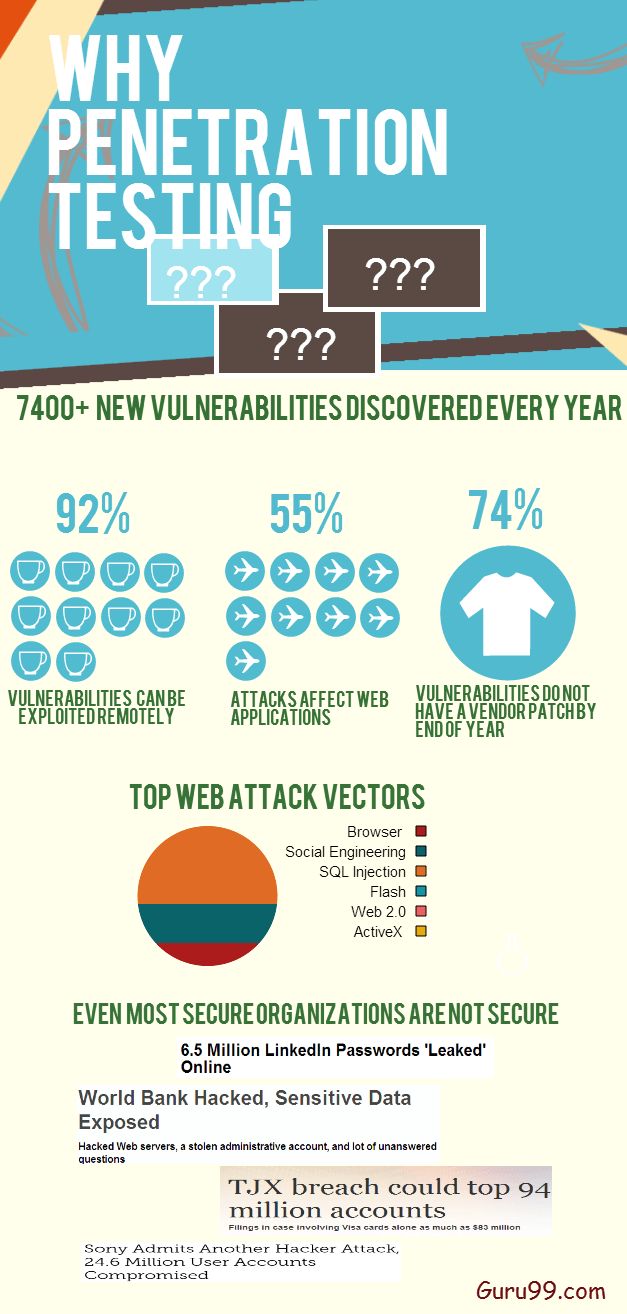
Why Penetration Testing?
Penetration is essential in an enterprise because –
- Financial sectors like Banks, Investment Banking, Stock Trading Exchanges want their data to be secured, and penetration testing is essential to ensure security
- In case if the software system is already hacked and the organization wants to determine whether any threats are still present in the system to avoid future hacks.
- Proactive Penetration Testing is the best safeguard against hackers
Types of Penetration Testing
The type of penetration test selected usually depends on the scope and whether the organization wants to simulate an attack by an employee, Network Admin (Internal Sources) or by External Sources. There are three types of Penetration testing and they are
- Black Box Testing
- White Box Penetration testing
- Grey Box Penetration Testing
In black-box penetration testing, a tester has no knowledge about the systems to be tested. He is responsible to collect information about the target network or system.
In a white-box penetration testing, the tester is usually provided with complete information about the network or systems to be tested including the IP address schema, source code, OS details, etc. This can be considered as a simulation of an attack by any Internal sources (Employees of an Organization).
In a grey box penetration testing, a tester is provided with partial knowledge of the system. It can be considered as an attack by an external hacker who had gained illegitimate access to an organization’s network infrastructure documents.
How to do Penetration Testing
Following are activities needs to be performed to execute Penetration Test –
Step 1) Planning phase
- Scope & Strategy of the assignment is determined
- Existing security policies, standards are used for defining the scope
Step 2) Discovery phase
- Collect as much information as possible about the system including data in the system, usernames and even passwords. This is also called as FINGERPRINTING
- Scan and Probe into the ports
- Check for vulnerabilities of the system
Step 3) Attack Phase
- Find exploits for various vulnerabilities You need necessary security Privileges to exploit the system
Step 4) Reporting Phase
- A report must contain detailed findings
- Risks of vulnerabilities found and their Impact on business
- Recommendations and solutions, if any
The prime task in penetration testing is to gather system information. There are two ways to gather information –
- ‘One to one’ or ‘one to many’ model with respect to host: A tester performs techniques in a linear way against either one target host or a logical grouping of target hosts (e.g. a subnet).
- ‘Many to one’ or ‘many to many’ model: The tester utilizes multiple hosts to execute information gathering techniques in a random, rate-limited, and in non-linear.
Examples of Penetration Testing Tools
There is a wide variety of tools that are used in penetration testing and the important Pentest tools are:
1) Teramind
Teramind delivers a comprehensive suite for insider threat prevention and employee monitoring. It enhances security through behavior analytics and data loss prevention, ensuring compliance and optimizing business processes. Its customizable platform suits various organizational needs, providing actionable insights that focus on boosting productivity and safeguarding data integrity.
Features:
- Insider Threat Prevention: Detects and prevents user actions that may indicate insider threats to data.
- Business Process Optimization: Utilizes data-driven behavior analytics to redefine operational processes.
- Workforce Productivity: Monitors productivity, security, and compliance behaviors of the workforce.
- Compliance Management: Helps manage compliance with a single, scalable solution suitable for small businesses, enterprises, and government agencies.
- Incident Forensics: Provides evidence to enrich incident response, investigations, and threat intelligence.
- Data Loss Prevention: Monitors and protects against the potential loss of sensitive data.
- Employee Monitoring: Offers capabilities to monitor employee performance and activities.
- Behavioral Analytics: Analyzes granular customer app behavior data for insights.
- Customizable Monitoring Settings: Allows customization of monitoring settings to suit specific use cases or to implement predefined rules.
- Dashboard Insights: Provides visibility and actionable insights into workforce activities through a comprehensive dashboard.
- NMap– This tool is used to do port scanning, OS identification, Trace the route and for Vulnerability scanning.
- Nessus– This is traditional network-based vulnerabilities tool.
- Pass-The-Hash – This tool is mainly used for password cracking.
Role and Responsibilities of Penetration Testers
Penetration Testers job is to:
- Testers should collect required information from the Organization to enable penetration tests
- Find flaws that could allow hackers to attack a target machine
- Pen Testers should think & act like real hackers albeit ethically.
- Work done by Penetration testers should be reproducible so that it will be easy for developers to fix it
- Start date and End date of test execution should be defined in advance.
- A tester should be responsible for any loss in the system or information during the Software Testing
- A tester should keep data and information confidential
Manual Penetration vs. automated penetration testing
| Manual Penetration Testing | Automated Penetration Testing |
|---|---|
| Manual Testing requires expert professionals to run the tests | Automated test tools provide clear reports with less experienced professionals |
| Manual Testing requires Excel and other tools to track it | Automation Testing has centralized and standard tools |
| In Manual Testing, sample results vary from test to test | In the case of Automated Tests, results do not vary from test to test |
| Memory Cleaning up should be remembered by users | Automated Testing will have comprehensive cleanups. |
Disadvantages of Penetration Testing
Penetration Testing cannot find all vulnerabilities in the system. There are limitations of time, budget, scope, skills of Penetration Testers
Following will be side effects when we are doing penetration testing:
- Data Loss and Corruption
- Down Time
- Increase Costs
Conclusion
Testers should act like a real hacker and test the application or system and needs to check whether a code is securely written. A penetration test will be effective if there is a well-implemented security policy. Penetration testing policy and methodology should be a place to make penetration testing more effective. This is a complete beginners guide for Penetration Testing.
Check our Live Penetration Testing Project